Cyber Security
CYBER SECURITY For Businesses, Schools & The Wider Public sector
“Breathe has been removing the cost, complexity and worry from Cyber Security since 2003”

Need to talk to an expert now?
Call: 01223 209920 – Cambs HQ
Call: 020 3519 0124 – London Office
Book Your Free Cyber Security Review worth £1200 today! – Available for a limited time only
Gain clarity and understand your Cyber Security Posture! Identify vulnerabilities, compliance gaps and risks — with certified experts trusted since 2003.
Our Accreditations
It’s a specialised industry and we have specialised knowledge. Not only of security best practices in general, but we have significant experiences and have deployed hundreds of solutions. Our consultants are certified by the vendors to ensure that these complex solutions are installed correctly and the configurations optimised to ensure your security.







- Managed Cyber Security Services (Outsourced or Co-Managed)
- Cyber Security Framework Implementation
- Security Risk Assessments
- Security Audits
- Penetration Testing
- Security Consultancy
- Cyber Security Awareness Training
- Assistance with Certifications such as ISO27001 or Cyber Essentials
- Security Product and Vendor selection. Helping you select the most suitable Security Solutions
- Procurement
- Implementation & Installation
- Backup, Business Continuity, Disaster Recovery
Trusted by over 400+ clients since 2003











How we help you…
Cyber Security Support For SME Businesses & Schools that outsource their IT
Our customers that outsource their IT are able to get the Breathe Team onboard, next to their existing IT Support Partner, expanding the overall capabilities or as a fully managed service where Breathe provides an integrated IT Support and Cyber Security service.
Our approach, is to remove the complexity, jargon and cost from Cyber Security for Business Owners and their Managers and for School Senior Leadership Teams.
We take care of the Cyber Security and ensure that you feel comfortable, with a team that you can Trust and rely on, while leaving you to focus on your day job.

Cyber Security Support For Businesses, Schools and Trusts that already have their own in-house IT Team
If you already have a good IT Team, it makes the job easier. Breathe provide Security Specialist engineers to extend your teams capabilities and reach, whilst providing them with advice, coaching and a sounding board.
Additionally, we provide:
- Penetration Testing & Phishing Attacks
- IT & Cyber Security Audits
- Secure System Design
- Provision and Procurement of Security Technologies such as Firewalls or End Point Security Licensing
- Project work and deployment services
- Backup Solutions and Cloud Storage
- Business Continuity and Failover Systems – Breathe has it’s own Private Cloud with independently owned Data Centres for hosting of backup and systems
- Cyber Security Service Desk and Engineering Visits
- Virtual CISO
- Post Incident Remediation

Our Cyber Security Methodology

Why would anyone want to hack my Business or School?
Financial gain (the most common)
Steal personal data / identity theft
Access to financial systems / invoice fraud
Credential harvesting / account takeover
Intellectual property / proprietary data theft
Sabotage / disruption (availability attacks)
Political/ideological motives (activism)
Children / grooming / exploitation
Testing/learning (script kiddies) and probing
Supply-chain compromise / indirect access
The Breathe Easy, Cyber Security Framework
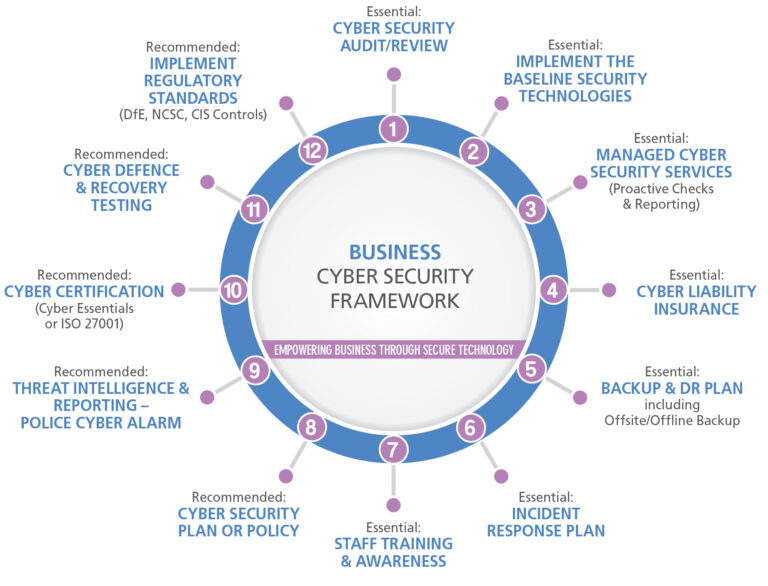
The Breathe Easy – Cyber Security Framework, has been designed by Breathe, to help simplify and remove the excessive costs from implementing a proven Cyber Security System, based on industry leading best practice from organisations like NCSC (National Cyber Security Centre .Gov), Cyber Essentials, Centre Of Internet Security(CIS Controls), DFE and the Chartered Institute Of Information Security.
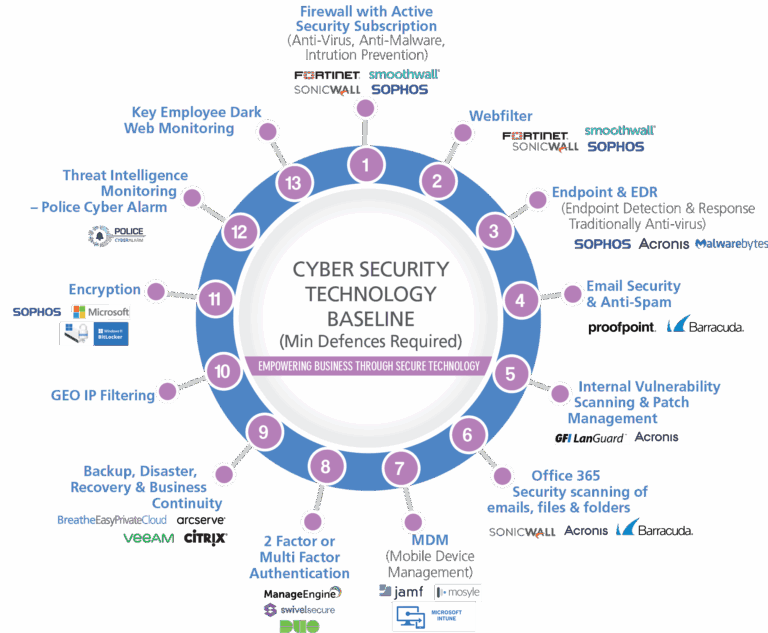
Our Cyber Security Technology Baseline
The Technology baseline we deploy for our customers provide what we believe to be the minimum categories of technologies that you should have in place to create defences, monitor your system and have an effective recovery solution in place.
Breathe have official partnerships with the vendor products we recommend. This ensures that you as our client, always receives the best possible pricing, support and installation services from an accredited Cyber Security Partner.
Our Cyber Security Product Portfolio
Office 365 Security

SonicWall CAS – Cloud Application Security provides a complete Office 365 Security Solution. Scanning of your data and anti malware protection for SharePoint, Team, Exchange and the other Office 365 Productivity Apps.
Helps businesses and schools deliver useful Internet usage reports to HR, Teachers, Department Managers and Administrators
Market Leading Email Security for all email solutions including Office 365 and G‑Suite. Anti-Spam, Anti-Virus and Malware, URL Scanning, Anti Phishing, DLP (Data Loss Prevention), Email Encryption and Archiving.
Market Leading Cyber Security for email. Sophos provides a dingle vendor solution to cover Email, Office 365, your Firewalls and End point Security.
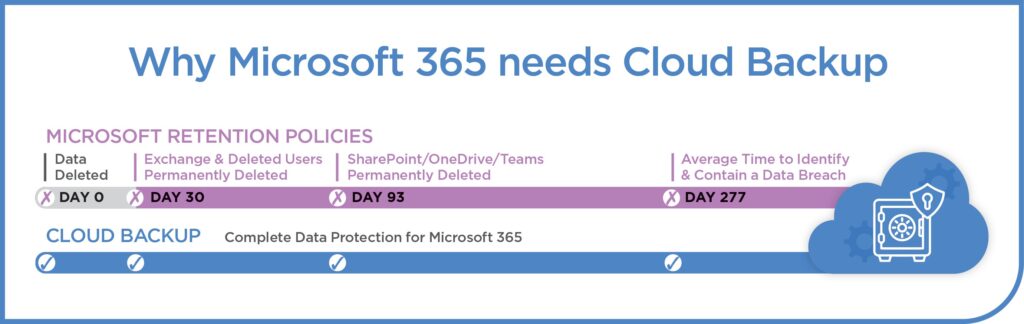
Backup for Office 365 including Email and Sharepoint. Cloud to Cloud or Cloud to On-Premise.

On-Prem & Cloud Firewalls

SonicWall next-generation firewalls give you the network security, control and visibility your organization needs to innovate and grow quickly.
Award-winning, enterprise-grade protection for SMBs and distributed enterprises in one cost-effective, centrally managed solution.
FortiGate next-generation firewalls (NGFWs) utilize purpose-built security processors and threat intelligence security services from AI-powered FortiGuard labs to deliver top-rated protection
XG Firewall offers the best protection against the latest advanced threats like ransomware, cryptomining, bots, worms, hacks, breaches and APTs
Patch Management & Vulnerability Scanning
Automatically discover all the elements of your network, scan your network for missing patches, and identify non-patch vulnerabilities with a list of 60,000+ known issues
Focussed on networks where devices connect to the LAN and staff work from the office regularly
Managed Engine has a huge repository of patches for most of your systems and applications. Often hackers use these Non-Microsoft applications as a back door because they know that the Microsoft systems are patched.
Focussed on networks that are Cloud based and it’s perfect for remote working staff.

End Point Protection (Anti-Virus & Anti Malware)
Delivers unmatched protection against unknown malware, exploits, and ransomware by combining cutting-edge technologies, such as deep learning and endpoint detection and response
Protects you against malware, ransomware, malicious websites, and other advanced online threats that have made traditional antivirus obsolete

Encryption

Bitlocker is an encryption feature for Microsoft Windows designed to protect data by providing encryption for entire volumes
Secure Remote Access

Empower your workforce with mobility and BYOD, and simplify access management when moving to the cloud. SonicWall Secure Mobile Access is a unified secure access gateway that provides best-in-class SSL VPN, context aware device authorization, application level VPN and advanced authentication. Now also with the latest cloud based VPN technologies that connect to your on-prem and Cloud IT, such as Azure.

Citrix Gateway provides secure delivery of Microsoft RDP/RDS. On establishing a full SSL VPN tunnel, users can access their remote desktops through a browser
Two Factor Authentication
Cisco DUO provides 2 factor and multi-factor authentication for identity storage and management with the scalability and security of Active Directory in a cost effective cloud based solution
Secure WiFi

SonicWall wireless network security products provide you with an enhanced wireless user experience by delivering the performance, range and reliability of 802.11ac and 802.11n wireless technologies with the SonicWave series access points
Customer-driven enterprise networking solutions that create stronger connections with customers, partners, and employees
Mobily Device Management
Mobile Device Management for Office 365 helps you secure and manage your users’ mobile devices like iPhones, iPads, Androids, and Windows phones
AirWatch is the leading enterprise mobility management technology that powers VMware Workspace ONE

Data & Email Archiving
Proofpoint Enterprise Archive is a cloud-based archiving solution that simplifies your legal discovery, regulatory compliance and end-user data access. It provides you with a secure and searchable central repository of a wide range of content types without the headaches of managing an email archive in-house.
Internet Filtering

Sonicwall Content Filtering Service provides administrators with the tools to create and apply policies that allow or deny access to sites based on individual or group identity, or by time of day, for over 50 predefined categories
Security Reporting
Helps businesses and schools deliver useful Internet usage reports to HR, Teachers, Department Managers and Administrators
Backup, Disaster Recovery & Business Continuity
Unlimited Backup for Office 365 including Email and Sharepoint. Cloud to Cloud or Cloud to On-Premise.

Helps businesses and schools deliver useful Internet usage reports to HR, Teachers, Department Managers and Administrators
SIEM & Event Management
SonicWall CAS – Cloud Application Security provides a complete Office 365 Security Solution. Scanning of your data and anti malware protection for SharePoint, Team, Exchange and the other Office 365 Productivity Apps.
Helps businesses and schools deliver useful Internet usage reports to HR, Teachers, Department Managers and Administrators
Threat Intelligence

Helps businesses and schools deliver useful Internet usage reports to HR, Teachers, Department Managers and Administrators
24/7 SOC – Security Operations Centre

SonicWall CAS – Cloud Application Security provides a complete Office 365 Security Solution. Scanning of your data and anti malware protection for SharePoint, Team, Exchange and the other Office 365 Productivity Apps.



